SOC Fundamentals
Summary
Description: A SOC, Security Operations Center, is a team of cyber security professionals (analysts) that continuously monitor an organization’s network 24/7.
Introduction to SOC
What is a SOC?
Security Operations Center (SOC) is a team of IT security professionals tasked with monitoring, preventing, detecting, investigating and responding to threats within a company’s network and systems.
Questions
What does the term SOC stand for?
Answer: Security Operations Center
Purpose and Components
Purpose
The SOC focuses on detecting vulnerabilities/intrusions and then respond accordingly to mitigate or prevent damage.
Components
 These are the pillars of a working SOC tea, these coexist to create a effective SOC.
These are the pillars of a working SOC tea, these coexist to create a effective SOC.
Questions
The SOC team discovers an unauthorized user is trying to log in to an account. Which capability of SOC is this?
Answer: Detection
What are the three pillars of a SOC?
Answer: People, Process, Technology
People
Importance of people
Having great tools like a SIEM is a good start, but software can only go so far. Without a real person checking the data, a SOC is basically guessing. You need a human to look at the alerts and decide what is an actual attack and what is just a mistake. Without that manual check, you’re just buried in noise.
SOC Roles
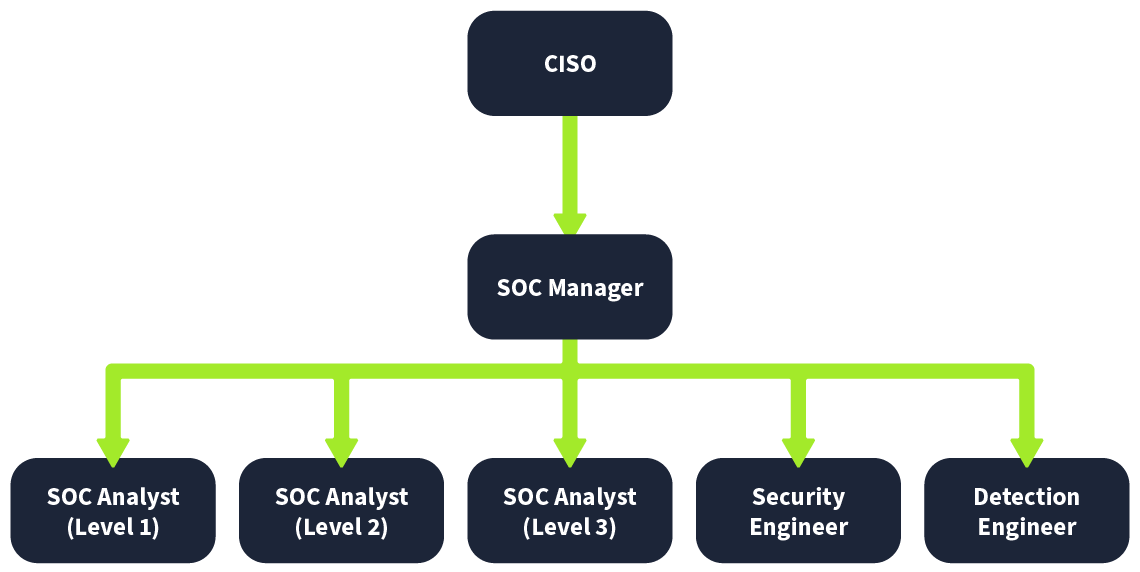
Explanation of the roles:
- SOC Analyst (Level 1): Anything detected by the security solution would pass through these analysts first. These are the first responders to any detection. SOC Level 1 Analysts perform basic alert triage to determine if a specific detection is harmful. They also report these detections through proper channels.
- SOC Analyst (Level 2): While Level 1 does the first-level analysis, some detections may require deeper investigation. Level 2 Analysts help them dive deeper into the investigations and correlate the data from multiple data sources to perform a proper analysis.
- SOC Analyst (Level 3): Level 3 Analysts are experienced professionals who proactively look for any threat indicators and support in the incident response activities. The critical severity detection reported by Level 1 and Level 2 Analysts are often security incidents that need detailed responses, including containment, eradication, and recovery. This is where Level 3 analysts’ experience comes in handy.
- Security Engineer: All analysts work on security solutions. These solutions need deployment and configuration. Security Engineers deploy and configure these security solutions to ensure their smooth operation.
- Detection Engineer: Security rules are the logic built behind security solutions to detect harmful activities. Level 2 and 3 Analysts often create these rules, while the SOC team can sometimes also utilize the detection engineer role independently for this responsibility.
- SOC Manager: The SOC Manager manages the processes the SOC team follows and provides support. The SOC Manager also remains in contact with the organization’s CISO (Chief Information Security Officer) to provide him with updates on the SOC team’s current security posture and efforts.
Questions
Alert triage and reporting is the responsibility of?
Answer: SOC Analyst (Level 1):
Which role in the SOC team allows you to work dedicatedly on establishing rules for alerting security solutions?
Answer: Detection Engineer
Process
Alert Triage
Triage is the process of analyzing the severity of an alert to help prioritization.
Malware Detected
HOST: GEORGE PC | STATUS: INFECTED
| 5 Ws | Answers |
|---|---|
| What? | A malicious file was detected on one of the hosts inside the organization’s network. |
| When? | The file was detected at 13:20 on June 5, 2024. |
| Where? | The file was detected in the directory of the host: “GEORGE PC”. |
| Who? | The file was detected for the user George. |
| Why? | After the investigation, it was found that the file was downloaded from a pirated software-selling website. The investigation with the user revealed that they downloaded the file as they wanted to use a software for free. |
Reporting
Incidents may be escalated if necessary to higher-level analysts. This could be done in form of tickets with a report that covers the 5 Ws with a analysis and pictures.
Incident Response and Forensics
If detections pose a critical threat, high-level teams initiate incident response.
Questions
At the end of the investigation, the SOC team found that John had attempted to steal the system’s data. Which ‘W’ from the 5 Ws does this answer?
Answer: Who
The SOC team detected a large amount of data exfiltration. Which ‘W’ from the 5 Ws does this answer?
Answer: What
Technology
SIEM
SIEM (Security Information and Event Management) bundles logs from various sources. Rules are created to identify suspicious activity, by correlating information from the logs rules are set off and create alerts. ML algorithms support detection capabilities.
SIEM only provides Detection
EDR
EDR (Endpoint Detection and Response) provides real-time and historical visibility into device activities. It operates at the endpoint level, allowing for detailed investigation and automated responses. With a few clicks, the SOC team can respond to threats directly on the machine.
EDR provides both Detection and Response
Firewall
A Firewall acts as a barrier between internal and external networks, such as the Internet. It monitors and filters incoming and outgoing traffic to block unauthorized access. Using specific detection rules, it identifies and stops suspicious traffic before it enters the internal network.
Firewall provides Prevention and Detection
There are more security solutions, these are the basic ones.
More solutions include Antivirus, EPP, IDS/IPS, SOAR, etc.
Questions
Which security solution monitors the incoming and outgoing traffic of the network?
Answer: Firewall
Do SIEM solutions primarily focus on detecting and alerting about security incidents? (yea/nay)
Answer: yea
Practical Exercise of SOC
Scenario
You are the Level 1 Analyst of your organization’s SOC team. You receive an alert that a port scanning activity has been observed on one of the hosts in the network. You have access to the SIEM solution, where you can see all the associated logs for this alert. You are tasked to view the logs individually and answer the question to the 5 Ws given below.
Note
The vulnerability assessment team notified the SOC team that they were running a port scan activity inside the network from the host:
10.0.0.8
Questions
What: Activity that triggered the alert?
Answer: Port Scan
When: Time of the activity?
Answer: June 12, 2024 17:24
Where: Destination host IP?
Answer: 10.0.0.3
Who: Source host name?
Answer: Nessus
Why: Reason for the activity? Intended/Malicious
Answer: Intended
Additional Investigation Notes: Has any response been sent back to the port scanner IP? (yea/nay)
Answer: yea
What is the flag found after closing the alert?
Answer: THM{000_INTRO_TO_SOC}